Listen To Our Podcast🎧
Account takeover fraud prevention in banks has become one of the most operationally demanding challenges in financial services. Attackers use credential stuffing bots, SIM swap attacks, and targeted phishing to seize customer accounts within minutes, often before a single alert fires. According to the FBI's Internet Crime Complaint Center (IC3), account takeover-related losses exceeded $2.9 billion in 2023, and that figure captures only what was reported.
The traditional playbook of rule-based alerts, manual review queues, and next-day reports breaks down when fraud moves at machine speed. What banks need is a combination of real-time fraud detection, machine learning, and automated decisioning that stops attacks before money leaves the account. This guide covers exactly how that works, which tools are worth evaluating, and where most institutions are still leaving gaps.
What Is Account Takeover Fraud and Why Banks Can't Ignore It
Account takeover fraud (ATO) occurs when an unauthorized party gains control of a customer's bank account, typically by stealing login credentials or bypassing authentication controls. Once inside, attackers move fast: they change contact details, initiate wire transfers, or drain funds through peer-to-peer payment rails before detection catches up.
Banks are the primary target because the payoff is direct and immediate. Unlike card fraud, where transactions can often be reversed, a successful ATO on a wire transfer is frequently irreversible. The financial damage is real; the customer trust damage runs deeper and takes years to recover.
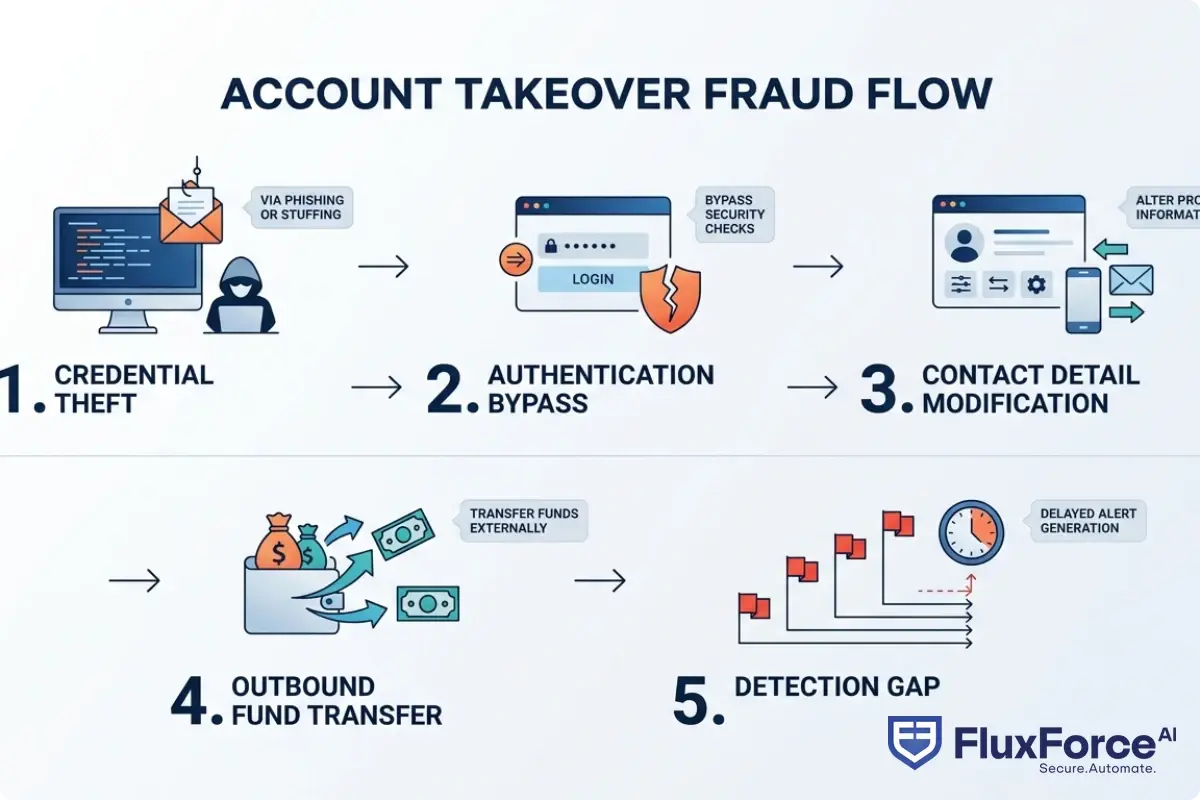
How Attackers Execute ATO Fraud
Modern ATO attacks are rarely manual. Most rely on:
- Credential stuffing: automated bots test billions of stolen username and password combinations from prior data breaches
- SIM swapping: social engineering telecom carriers to redirect a customer's phone number, bypassing SMS-based two-factor authentication
- Adversary-in-the-middle (AiTM) phishing: real-time proxy attacks that capture session tokens even when MFA is active
- Synthetic identity fraud: creating fictitious personas that pass KYC checks, then aging accounts before committing high-value transactions
The combination of automation and stolen data means a single threat actor can test thousands of accounts per hour. Rule-based systems that trigger on three consecutive failed logins simply cannot keep pace with that volume.
The Scale of the Problem
Javelin Strategy & Research estimates that ATO fraud losses in the US financial sector reached $13 billion in 2023, a figure that includes direct losses, operational remediation, and customer churn. For mid-size regional banks, a single high-profile ATO incident can generate six to eight weeks of manual review backlog and cost upward of $500,000 in recovery operations alone. That arithmetic makes account takeover fraud prevention in banks not just a security concern but a business continuity issue.
How AI Fraud Detection Works in Banking
AI fraud detection in banking applies machine learning models, behavioral analytics, and graph analysis to identify fraudulent activity without relying on static rule sets that attackers have long since learned to evade. AI fraud detection explained simply: legitimate customers behave consistently. Their devices, locations, transaction amounts, and session timing form a behavioral fingerprint. AI maps that fingerprint and flags deviations that no fixed rule would ever catch.
Machine Learning Fraud Detection: Beyond Simple Rules
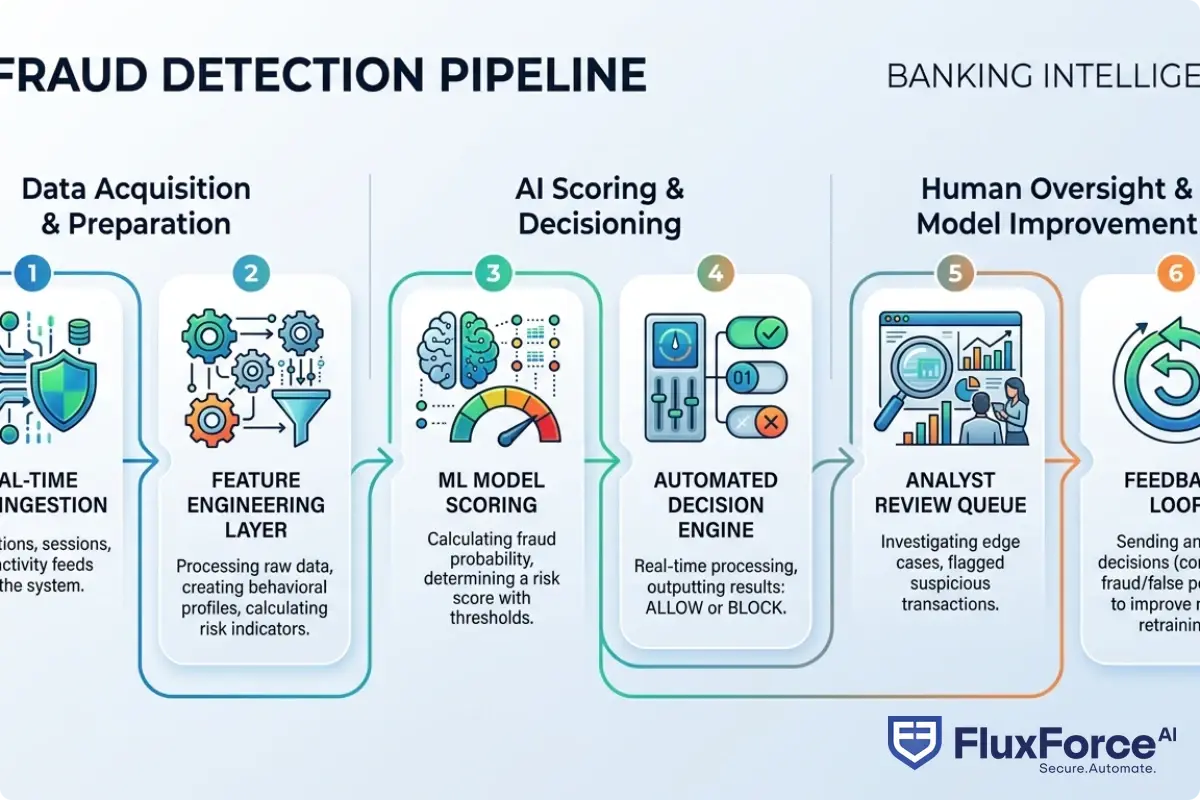
Machine learning fraud detection works by training statistical models on historical transaction and session data labeled as fraudulent or legitimate. The model learns which feature combinations predict fraud and updates continuously as patterns shift.
Three model types power most banking deployments today:
- Supervised learning models (gradient boosting, neural networks): trained on labeled fraud data, producing high precision on known fraud patterns
- Unsupervised anomaly detection: flags unusual behavior even without labeled examples, useful for catching novel attack patterns
- Graph neural networks: map relationships between accounts, devices, and IP addresses to surface fraud rings and mule account networks
How does AI detect fraud in practice? Consider a customer who normally logs in from Chicago on an iPhone but suddenly authenticates from a country they have never visited, at 3 AM, through a browser they have never used before, and immediately initiates a $9,800 ACH transfer just below reporting thresholds. A rule-based system may miss this entirely. A machine learning model trained on behavioral features will score it as high-risk within milliseconds.
Real-Time Fraud Detection: Decisioning in Milliseconds
Real-time fraud detection means a risk score is calculated and a decision is made before a transaction completes, not after. This is the critical distinction from batch or near-real-time processing, where fraud is caught only after money has already moved.
For real-time fraud detection banks deploy at scale, the technical requirements are demanding: models must score a transaction in under 100 milliseconds, the decision engine must integrate with the core banking system mid-transaction, and the platform must handle peak volumes without latency degradation. Most cloud-native transaction monitoring software achieves this through streaming architectures like Apache Kafka, pre-computed feature stores, and inference APIs that return scores within 20 to 50 milliseconds.
Real-time fraud detection banks rely on today differs substantially from what was possible five years ago. The shift from overnight batch processing to sub-second decisioning is what makes the difference between catching fraud before funds leave and chasing them after.
AI Fraud Detection Software: Key Capabilities
When evaluating AI fraud detection software, the capabilities that matter most are:
| Capability | Why It Matters |
|---|---|
| Real-time decisioning | Stops fraud before funds leave the account |
| Behavioral biometrics | Detects ATO even when credentials are valid |
| Device intelligence | Flags emulators, VPNs, and spoofed devices |
| Case management integration | Reduces analyst workload through automated triage |
| Model explainability | Required for regulatory exams and SAR filing |
| Feedback loop automation | Model retrains as new fraud patterns emerge |
Fraud Alert Fatigue Is Quietly Draining Your Fraud Team
Fraud alert fatigue is the operational state where analysts receive so many alerts, the overwhelming majority of them false positives, that they start dismissing cases without proper review. It is one of the most underreported risk factors in banking fraud operations.
In traditional rule-based systems, false positive rates typically run between 90% and 97%. That means for every 100 fraud alerts generated, only 3 to 10 represent actual fraud. An analyst team reviewing 1,000 alerts per day spends most of their time closing tickets on legitimate customer activity.
This creates a dangerous feedback loop: analysts start speeding through reviews to keep up with volume, and genuinely suspicious cases get inadequate attention. Fraud slips through not because the system failed to flag it, but because the team was too stretched to investigate properly.
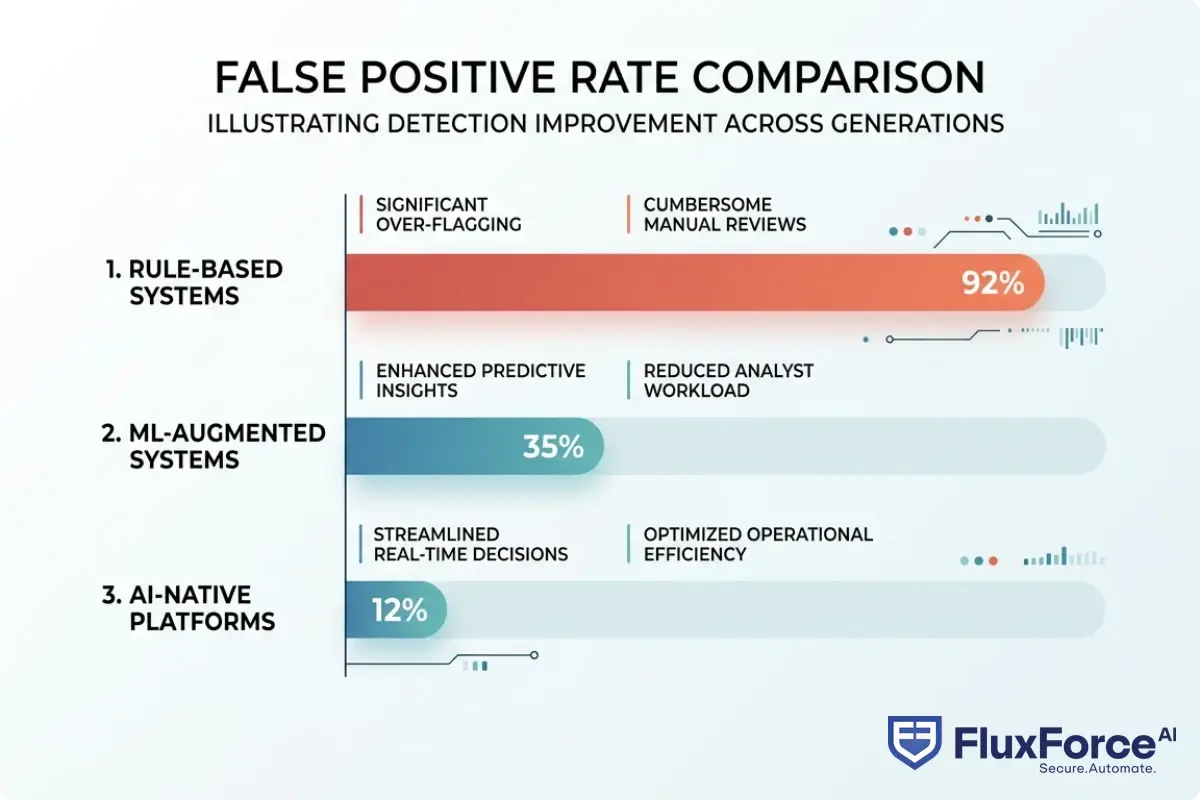
The False Positive Rate Problem
False positive rate fraud detection is the percentage of flagged transactions that turn out not to be fraudulent. High rates carry direct customer consequences beyond analyst burnout.
When a legitimate customer's transaction is blocked or their account frozen unexpectedly, they notice. A 2023 survey by Aite-Novarica found that 40% of bank customers who experienced a false fraud block seriously considered switching institutions. In competitive retail banking markets, that is a tangible retention risk that compounds over time.
For a detailed look at how agentic AI cuts false positive volumes by up to 80%, see How Agentic AI Fraud Agents Cut False Positives by 80%.
False Positive Cost Fraud Operations Bear
False positive cost in fraud operations is rarely calculated in full. Most teams measure analyst hours on alert reviews, but the complete picture includes:
- Analyst salaries and overhead ($0.80 to $2.00 per reviewed alert in most institutions)
- Customer service escalations from blocked legitimate transactions
- Lost revenue when customers abandon purchases after an unexpected decline
- Regulatory attention if SAR filing patterns suggest systematic over-flagging
A bank processing 500,000 transactions daily with a 90% false positive rate and a $1.20 per-alert review cost is spending roughly $540,000 per month reviewing alerts that are not fraud. That arithmetic accelerates the business case for automated transaction monitoring software considerably.
How to Reduce False Positives in AML and Transaction Monitoring
How to reduce false positives in AML starts with accepting that the problem is architectural, not operational. Hiring more analysts to review more alerts scales costs linearly while the root cause remains unchanged.
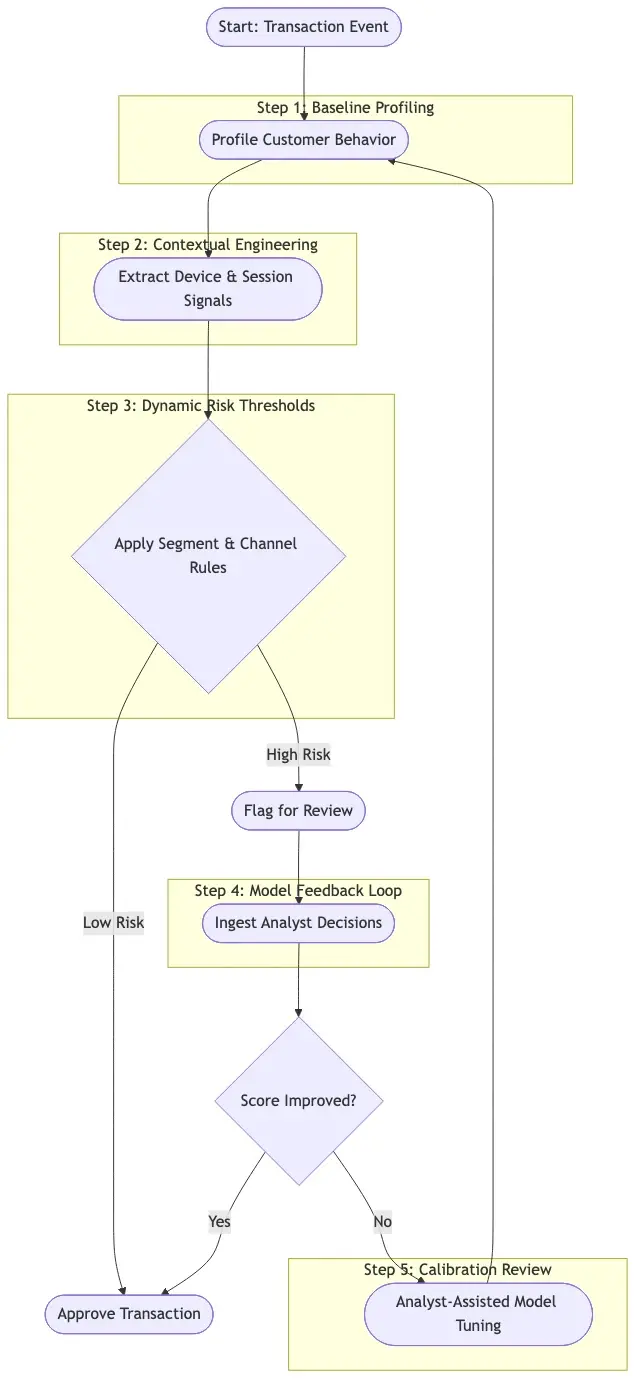
The shift that works is moving from static rule thresholds to dynamic, risk-scored decisioning. Instead of triggering an alert every time a transaction exceeds $5,000, a model evaluates the customer's behavioral history, the counterparty reputation, the device, the location, and the session context together, then flags the transaction only if the combined risk score exceeds a threshold calibrated to the institution's risk appetite.
Reduce False Positives Transaction Monitoring With ML
The most effective strategies to reduce false positives in transaction monitoring include:
- Customer segmentation models: different risk thresholds for different customer profiles rather than applying one universal rule across all accounts
- Contextual feature engineering: include device signals, session behavior, and counterparty risk in the score alongside transaction amount
- Continuous model retraining: monthly or weekly retraining cycles as attack patterns and customer behavior shift seasonally
- Human-in-the-loop feedback: analyst decisions on edge cases feed back into model retraining, improving precision over successive iterations
For a side-by-side comparison of rule-based approaches versus AI in this specific context, Reducing False Positives: Rule-Based Systems vs. AI-Driven Solutions covers the tradeoffs in practical detail.
What a Good False Positive Rate Fraud Detection Looks Like
A mature AI-powered program should target a false positive rate below 15% in high-risk transaction channels and below 30% across all transaction monitoring categories. Some best-in-class fintechs operate below 10% on card-not-present fraud. Getting there takes 6 to 12 months of model tuning and feedback loop maturation, it does not happen on day one.
The honest tradeoff: pushing false positive rates extremely low (below 5%) often increases false negatives, meaning real fraud that slips through undetected. The balance between catching more fraud and inconveniencing fewer customers is a tunable parameter, not a solved problem. Your institution's risk appetite and regulatory context should drive where you set that threshold.
How Account Takeover Fraud Connects to Payment Fraud Prevention and Synthetic Identity Fraud
Account takeover fraud and payment fraud prevention are increasingly intertwined in how banks experience them. ATO is often the first step in a broader fraud chain: a compromised account funds a payment that flows through a mule network, frequently built on synthetic identities that passed initial KYC screening.
Detecting Synthetic Identity Fraud in Real-Time explains how these synthetic personas are constructed. The short version: synthetic identity fraud uses real Social Security numbers, often from minors or deceased individuals, combined with fabricated names and addresses to pass identity verification. When these accounts receive ATO-sourced funds, they appear legitimate to first-order transaction monitoring.
Why Synthetic Identity Fraud Deserves Its Own Detection Layer
Synthetic identity fraud does not behave like traditional fraud. There is no victim to file a complaint. The synthetic persona passes AML screening. The account ages normally for months before any high-value activity appears. Standard transaction monitoring focused on behavioral anomalies misses this pattern entirely because each individual action looks routine.
Graph analytics that map relationships across account networks, shared addresses, phone numbers, devices, and email domains, can surface connected synthetic personas even when individual accounts appear clean. This is where AI vs. Traditional Fraud Detection: Key Differences Every Risk Officer Should Know demonstrates the clearest performance gap between legacy and modern approaches. Graph-based signals are essentially invisible to rule-based systems.
Transaction Monitoring Cost vs. Risk: Finding the Right Balance
Transaction monitoring cost is real, and institutions rightly ask whether expanded monitoring justifies the investment. The answer depends on the channel and customer segment. High-value wire corridors and P2P payment rails justify the highest monitoring intensity. Low-value recurring payments to known payees carry a different risk profile and do not need the same scrutiny.
Automated transaction monitoring platforms let risk teams configure channel-specific models rather than applying uniform rules everywhere. This approach controls transaction monitoring cost while keeping detection rates high where it actually matters. According to FinCEN's guidance on effective AML programs, risk-based approaches to monitoring are not just operationally sensible but regulatorily expected for covered financial institutions.
Sardine vs Unit21: Best Tools for Account Takeover Fraud Prevention in Banks
The sardine vs unit21 comparison comes up frequently in bank technology evaluations because both platforms represent mature, well-funded approaches to AI fraud detection software, and they make different architectural bets that favor different institutional profiles.
Sardine focuses heavily on device intelligence and behavioral biometrics at the session level. Its fraud scores incorporate over 4,000 signals per session, making it particularly effective against ATO attacks where credentials are already compromised. It suits mobile-first banks and fintechs with high transaction volumes and a need for pre-authentication fraud signals.
Unit21 emphasizes workflow automation and case management alongside detection, making it a better fit for banks with large analyst teams that need to reduce manual review workload. Its no-code rules engine allows compliance teams to adjust detection logic without engineering involvement, which matters for institutions that need rapid rule iteration during active fraud campaigns.
Neither is universally better. The right choice depends on whether your primary gap is detection accuracy, analyst efficiency, or both. In practice, most evaluations come down to integration complexity with the existing core banking stack and total cost of ownership rather than raw model performance differences.
For card-specific fraud detection strategy, Card Fraud Analytics: AI-Powered Fraud Detection Strategy for Risk Heads covers how to structure detection around your actual transaction mix.
What to Look for in AI Fraud Detection Software
When evaluating AI fraud detection software specifically for account takeover fraud prevention in banks, prioritize:
- Sub-100ms scoring latency for real-time channel integration without degrading transaction experience
- Explainable model outputs with feature attribution, which is critical for examiner inquiries and SAR documentation
- Pre-built integrations with your core banking platform and identity verification provider
- Feedback loop tooling so analyst review decisions improve model performance over time
- Regulatory reporting support including SAR filing templates and examination-ready audit logs
According to NIST's AI Risk Management Framework, explainability and bias monitoring are increasingly expected in regulated AI applications, and fraud detection is no exception. Build the governance overhead into your total cost of ownership calculation from the start rather than treating it as an afterthought.
AI fraud detection in banking is not a set-and-forget deployment. The threat evolves, the model needs to evolve with it, and the team needs tooling that makes continuous improvement practical.
Onboard Customers in Seconds

Conclusion
Account takeover fraud prevention in banks requires more than better rules. It requires a different architecture built on machine learning, behavioral analytics, and real-time decisioning that operates faster than any manual process can. The institutions winning this fight are not necessarily the ones with the largest fraud teams. They are the ones who have automated routine decisioning so analysts focus on the edge cases that genuinely need human judgment.
Invest in AI fraud detection in banking, reduce your false positive rate aggressively, and connect your ATO detection layer to your payment fraud prevention and synthetic identity fraud capabilities. These threats do not operate in silos, and your detection program should not either.
Start with the highest-risk channel, wire transfers, P2P payments, or new account origination, and build out from there. Trying to deploy across every channel simultaneously is the fastest path to a failed rollout and a demoralized team.
Frequently Asked Questions
AI fraud detection is the use of machine learning models, behavioral analytics, and graph analysis to identify fraudulent activity automatically, without relying on static rule sets. In banking, AI fraud detection analyzes thousands of signals per transaction — including device type, geographic location, session behavior, and transaction history — to calculate a real-time risk score and make automated block or allow decisions in under 100 milliseconds.
AI detects fraud in banking by building a behavioral baseline for each customer and flagging significant deviations from that baseline. Machine learning models trained on labeled fraud data learn which combinations of features predict fraud. When a transaction or login event deviates from a customer's established pattern — for example, an unrecognized device, unusual geography, or atypical transaction amount — the model assigns a high risk score and triggers a review or automatic block before the transaction completes.
Machine learning fraud detection uses statistical models trained on historical transaction data to predict whether new transactions are fraudulent. Unlike rule-based systems that trigger alerts based on fixed conditions, machine learning models weigh dozens to thousands of features simultaneously and update continuously as new fraud patterns emerge. Common model types include gradient boosting classifiers, neural networks for pattern recognition, and graph neural networks for surfacing connected fraud networks.
Real-time fraud detection means a fraud risk score is calculated and a decisioning outcome is produced before a transaction completes, typically within 20 to 100 milliseconds. This requires streaming data architectures, pre-computed feature stores, and inference APIs integrated directly with the core banking system. The alternative — batch or near-real-time processing — catches fraud only after funds have already moved, making recovery significantly harder.
AI fraud detection software is a technology platform that applies machine learning models to transaction and behavioral data to identify fraud in real time. Key capabilities include real-time risk scoring, behavioral biometrics, device intelligence, model explainability for regulatory compliance, case management integration to reduce analyst workload, and feedback loop automation so the model improves as analysts review edge cases. Examples evaluated by banks include Sardine and Unit21.
Banks reduce false positives in AML by replacing static rule thresholds with dynamic, context-aware risk scoring that considers device signals, session behavior, counterparty reputation, and customer history alongside transaction amount. Effective strategies include customer segmentation models with separate thresholds per profile, continuous model retraining on a monthly or weekly cadence, and analyst feedback loops that feed review decisions back into model improvement. Well-tuned AI systems achieve false positive rates below 15% in high-risk channels, compared to 90 to 97% in traditional rule-based systems.
False positive cost in fraud operations includes analyst time reviewing non-fraudulent alerts (typically $0.80 to $2.00 per alert), customer service escalations from blocked legitimate transactions, lost revenue when customers abandon purchases after an unexpected decline, and potential regulatory scrutiny if SAR filing patterns suggest systematic over-flagging. Banks processing high transaction volumes with 90% false positive rates can spend hundreds of thousands of dollars monthly reviewing alerts that are not fraud.




Share this article