Listen To Our Podcast🎧
Behavioral biometrics fraud prevention is changing how financial institutions separate legitimate customers from fraudsters. Static credentials like passwords and PINs tell you what someone knows. They say nothing about how that person types, holds their phone, or hesitates at a field they should know by heart. Fraudsters who buy stolen credentials bypass authentication without triggering a single alert. Banks responding with more rules drive up fraud alert fatigue and analyst burnout. Meanwhile, synthetic identity fraud and account takeover attacks continue climbing. This post breaks down how behavioral biometrics works, where it fits into an AI fraud detection stack, and what it takes to cut false positives without missing real threats.
What Does Behavioral Biometrics Actually Measure?
Behavioral biometrics captures the unconscious habits that define how a specific person interacts with a device. Unlike fingerprints or face scans captured once as a static template, behavioral signals are continuous. They update every session and adapt as the system learns more about a user's normal patterns.
Typing Patterns, Mouse Dynamics, and Device Interaction
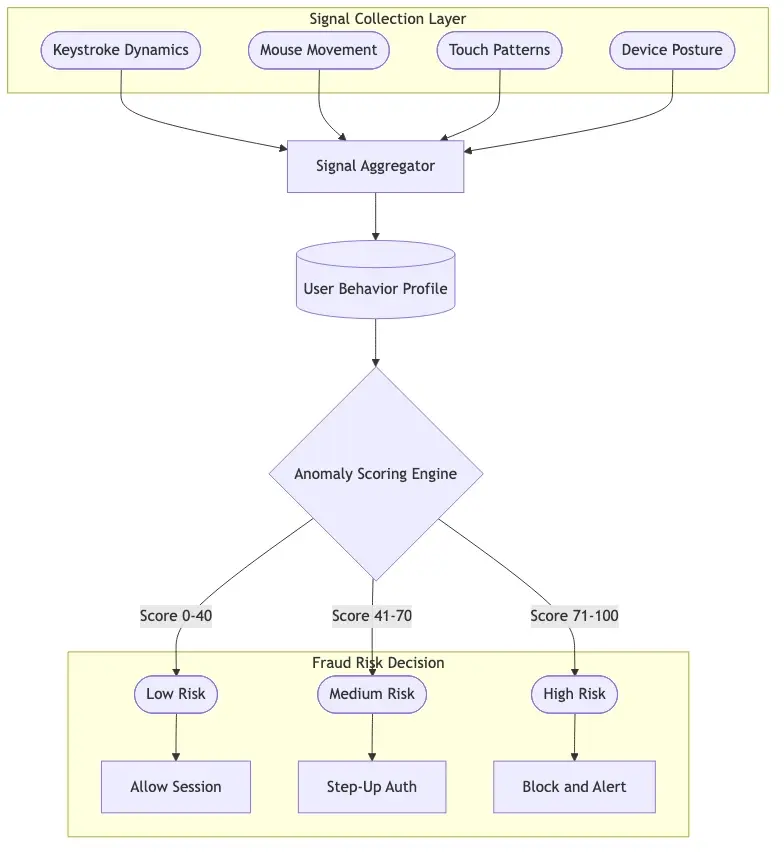
The core signals include:
- Keystroke dynamics: rhythm, dwell time (how long each key is held), and flight time (the gap between keystrokes)
- Mouse movement: speed, acceleration, trajectory, and click pressure
- Touch behavior on mobile: swipe velocity, finger pressure, grip orientation, and tap rhythm
- Device posture: how a person holds their phone, gyroscope readings, and screen tilt angle
None of these signals matter in isolation. The system builds a probabilistic model of each user's behavior over dozens or hundreds of sessions. A fraudster using stolen credentials might enter the right password, but their typing rhythm will differ completely from the account owner's established pattern.
How Behavioral Data Differs From Static Identifiers
A password can be phished in 30 seconds. A behavioral profile built across six months of banking sessions cannot be replicated by someone who bought access on a dark web market. That difference makes behavioral biometrics particularly useful for catching account takeover attacks that have already defeated authentication. The system does not just ask "do you know the right password?" It asks "are you the person who has always logged in this way?"
How Behavioral Biometrics Fraud Prevention Works With AI Detection
Behavioral biometrics fraud prevention is one layer in a broader AI fraud detection stack that combines device intelligence, transaction history, network signals, and identity verification. The combination matters because each data source catches a different fraud pattern.
Machine Learning Fraud Detection Models That Learn User Behavior
Machine learning fraud detection models analyze behavioral signals alongside hundreds of other features to produce a risk score per session. They are trained on historical patterns: what does a normal login look like for this user, device, and time of day? A rule-based system flags any login from a foreign IP. An ML model recognizes that this user logs in from three countries regularly because they travel, so the foreign IP alone is low risk. That nuance is where AI vs. traditional fraud detection shows its clearest advantage.
AI Fraud Detection Explained: From Signal to Decision
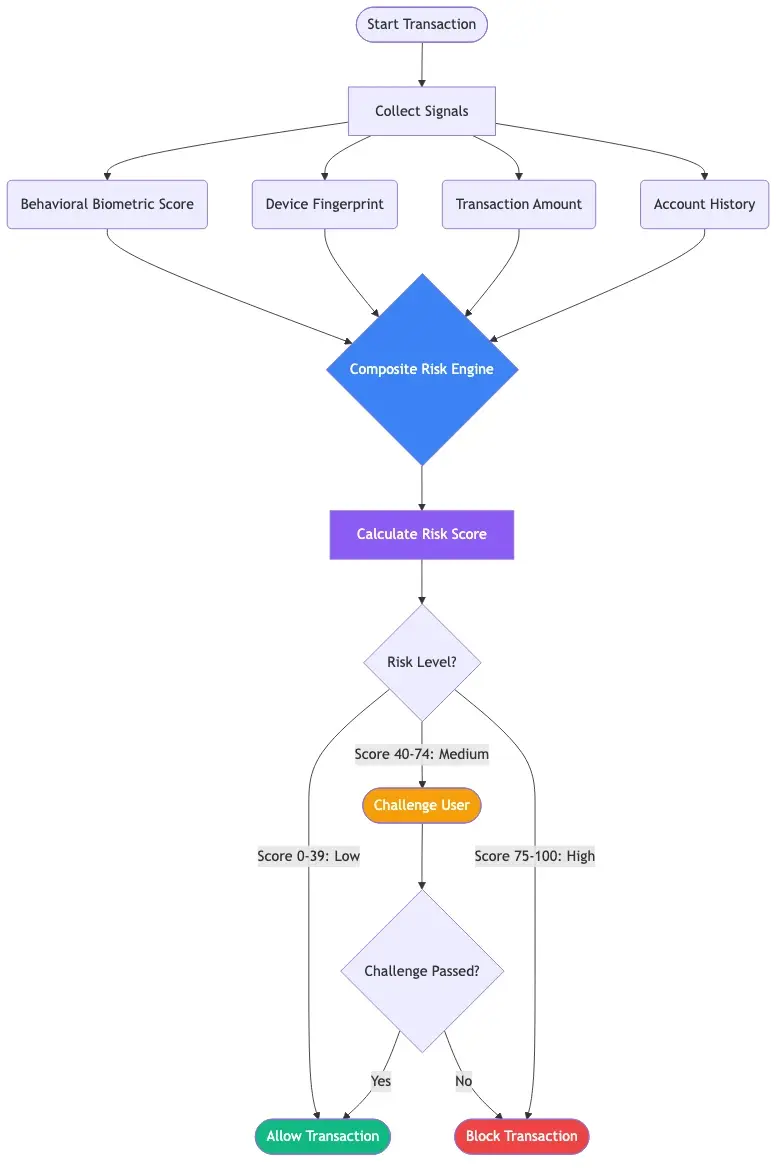
AI fraud detection combines supervised learning, unsupervised anomaly detection, and reinforcement learning. Here is the flow:
- Session signals are collected in real time: keystroke dynamics, mouse patterns, device telemetry
- Features are extracted and normalized against the user's historical baseline
- The ML model scores the session against the behavioral profile
- The score is combined with transaction context: amount, merchant category, location
- The composite risk score triggers an allow, challenge, or block action automatically
This is ai fraud detection explained at its core: continuous signal ingestion, model scoring, and an automated decision completing in under 200 milliseconds.
How Does AI Detect Fraud Using Behavioral Signals?
How does AI detect fraud when a fraudster has valid credentials? It looks at everything credentials cannot reveal. The fraudster copy-pasted the password rather than typing it. They moved the mouse in straight lines, which real users almost never do. They navigated directly to wire transfer without visiting account summary first, which the real account holder always does. Any single signal is weak evidence. Combined, they are strong.
Why Passwords Leave Payment Fraud Prevention Gaps
Passwords are a shared-secret model designed for a world where attackers could not efficiently scale credential testing. Credential stuffing tools now test thousands of combinations per minute against banking login pages without friction.
Credential Stuffing and Account Takeover Rates
The FBI's Internet Crime Complaint Center reported over $10.3 billion in cybercrime losses in 2022, with account takeover driving a significant share. A fraudster purchasing a 500,000-credential list and achieving a 2-5% success rate has up to 25,000 compromised accounts from a single dataset. SIM-swapping defeats SMS OTP. Social engineering defeats authenticator apps. Beyond credential theft, banks also face synthetic identity fraud that bypasses traditional KYC entirely because the fraudster is not impersonating anyone who exists.
Where Payment Fraud Prevention Breaks Down
Payment fraud prevention relying on static controls consistently fails at three points: after authentication (session hijacking), during session handoff (a bot continuing a session a human started), and at new device onboarding (adding a mule device to a compromised account). Behavioral biometrics addresses all three because it scores the full session continuously, not just the login event.
How Real-Time Fraud Detection Works in Banking
Most fraud decisions in banking happen in well under a second. That speed requirement shapes how behavioral biometrics integrates into a fraud stack, and why the choice of transaction monitoring software matters as much as the underlying models.
Real-Time Fraud Detection Banks Use at Transaction Speed
Real-time fraud detection banks implement typically involves a low-latency scoring API between the user's session and the authorization system. When a customer initiates a payment, the fraud engine scores behavioral signals, device fingerprint, and transaction details simultaneously. The entire exchange takes 50-150 milliseconds on well-optimized stacks.
Real-time fraud detection is most effective when behavioral biometrics pair with AI-powered card fraud analytics tracking spending patterns across the full account history. Neither works as well alone.
Reduce False Positives in Transaction Monitoring With Behavioral Context
Behavioral context is one of the most underused levers for reducing false positives in transaction monitoring. A rule-based system flags any transfer over $5,000 to a new payee. With behavioral biometrics, the system sees that the user navigated to payee setup using their normal typing rhythm and confirmed through their usual interaction pattern. That behavioral confidence score suppresses the false positive without analyst involvement. The right transaction monitoring software exposes behavioral confidence as a direct input to alert triage rather than a separate silo.

The False Positive Problem in Automated Transaction Monitoring
Fraud alert fatigue is the quiet operational cost of over-sensitive detection. When analysts see too many false positives, they clear alerts faster and with less scrutiny. Real fraud slips through not because the model missed it, but because the analyst reviewing it has cleared 200 near-identical false alarms that week.
The False Positive Cost Fraud Teams Actually Pay
False positive cost fraud teams carry is larger than most risk officers realize. Manual review costs $15-50 per alert depending on analyst seniority. A team processing 10,000 monthly alerts at an 85% false positive rate spends $127,500 to $425,000 per month on clean transactions. That is transaction monitoring cost before accounting for churn from declined legitimate customers.
The false positive rate fraud detection benchmark at rule-heavy institutions often exceeds 95%, meaning fewer than 1 in 20 alerts is real fraud.
How to Reduce False Positives in AML Without Losing True Detections
How to reduce false positives in AML takes better signals and smarter thresholds. Behavioral biometrics improves signal quality at the session level. Automated transaction monitoring with ML models adjusts thresholds dynamically rather than locking in static rules. Well-tuned ML systems cut false positive rates to 70-80%, and behavioral biometrics pushes that lower still for account takeover scenarios. See how agentic AI fraud agents cut false positives by 80% and reducing false positives: rule-based vs. AI-driven solutions for operational detail.
How Behavioral Biometrics Stops Synthetic Identity Fraud
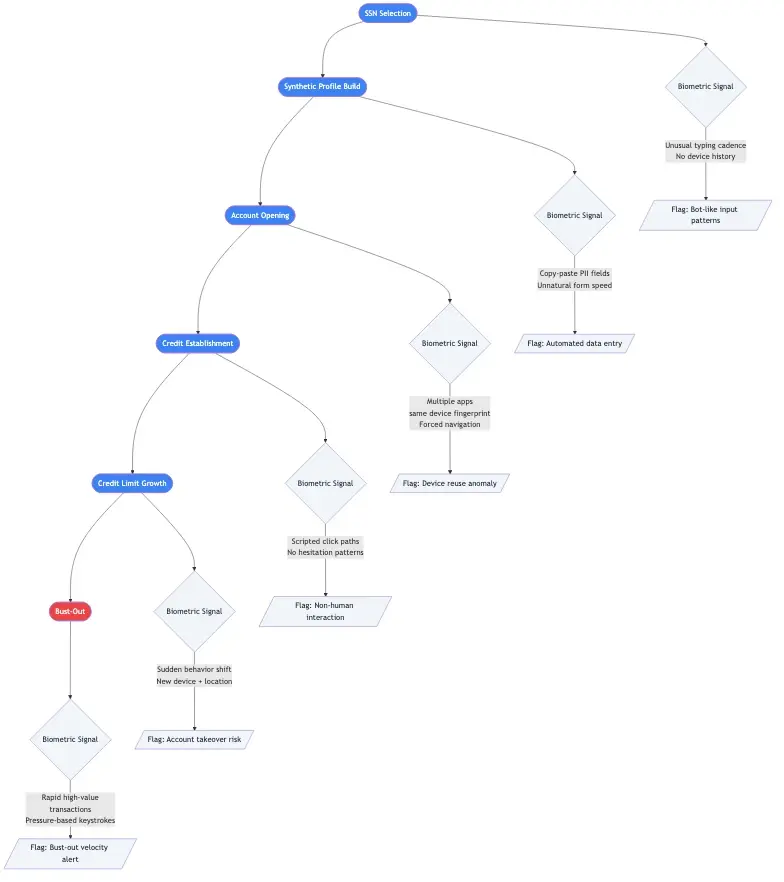
Synthetic identity fraud is the fastest-growing fraud type in financial services. Unlike traditional identity theft, synthetic identity fraud combines real and fabricated data to create a person who does not exist. These personas are built over months before the fraud event.
What Synthetic Identity Fraud Looks Like in Practice
A synthetic identity fraudster uses a real SSN (often a child's) with a fabricated name and address, opens a credit account, builds a thin credit history over 6-18 months, then busts out: maxes all credit lines and disappears. Traditional KYC passes because the SSN is real. The Federal Reserve's whitepaper on synthetic identity fraud estimated U.S. losses at $6 billion annually, likely understated because synthetic identities are often classified as credit losses rather than fraud.
AI Fraud Detection in Banking for Synthetic Identities
AI fraud detection in banking addresses synthetic identity fraud at onboarding and post-account-opening. During application, behavioral biometrics flags sessions where the applicant pauses longer at fields they must look up rather than recall naturally. After opening, ai fraud detection in banking monitors for atypical patterns: quiet for months, then sudden high transaction velocity before bust-out. For detection tactics in practice, detecting synthetic identity fraud in real-time covers the signals and models used.
Choosing AI Fraud Detection Software: Sardine vs Unit21 and Beyond
Evaluating ai fraud detection software is harder than vendor marketing suggests. Every platform claims real-time AI detection. The differences that matter are latency guarantees, false positive benchmarks on realistic data, behavioral biometrics depth, and integration with existing transaction monitoring software.
Sardine vs Unit21: What Each Does Well
Sardine vs Unit21 surfaces frequently at mid-market banks and fintechs. Sardine is device-and-behavior-first, capturing deep behavioral signals at session start for account takeover and bot detection. Unit21 is a case management and rules platform with strong analyst workflow tooling for teams needing structured review and flexible rule customization. Many institutions run both or look for platforms integrating behavioral biometrics into a broader orchestration layer.
The right fraud detection software integrates behavioral signals directly into the transaction scoring pipeline rather than treating them as a separate layer, which is the key distinction to test during any proof of concept.
Evaluating Transaction Monitoring Cost vs. Capability
Transaction monitoring cost means nothing without knowing fraud losses prevented and analyst hours saved. A platform at $0.01 per transaction across 50 million monthly transactions costs $500,000 per month. Demand proof-of-concept results on your own data, not published benchmarks, because behavioral biometrics performance varies significantly by customer demographics and device mix. NIST's biometrics testing resources provide useful frameworks for evaluating vendor accuracy claims around false rejection and false acceptance rates.
Onboard Customers in Seconds

Conclusion
Behavioral biometrics fraud prevention closes the gap that passwords, PINs, and static authentication leave wide open. Behavioral systems catch account takeovers, synthetic identity fraud, and session hijacking that rule-based controls miss entirely. The reduction in false positives matters equally: when behavioral context feeds into transaction monitoring decisions, analysts spend time on genuine fraud signals rather than clean transactions.
This directly addresses fraud alert fatigue, which raises transaction monitoring cost and degrades analyst performance over time. Test behavioral biometrics on account takeover scenarios first, where the signal advantage is clearest, then expand to onboarding and payment fraud prevention. The institutions moving fastest treat behavioral signals as a core data source from day one, not an optional layer added later.
Frequently Asked Questions
AI fraud detection is the use of machine learning models to identify fraudulent transactions, account takeovers, and synthetic identity fraud in real time. Unlike rule-based systems that flag transactions on fixed thresholds, AI fraud detection learns from historical patterns and adapts to new fraud tactics without manual rule updates. It is used in banking, fintech, and insurance to reduce fraud losses and the false positive rates that drive fraud alert fatigue.
AI fraud detection explained simply: the system collects signals from each user session including behavioral biometrics, device fingerprint, and transaction details, feeds them into a machine learning model, and produces a risk score within milliseconds. If the score exceeds a threshold, the transaction is blocked or stepped up to additional verification. The model learns continuously from analyst feedback, improving at separating real customers from fraudsters over time.
AI detects fraud by analyzing hundreds of behavioral, transactional, and contextual signals simultaneously. For behavioral biometrics, it compares how a user interacts with their device during the current session against a learned baseline from previous legitimate sessions. Deviations such as different typing rhythm, unusual mouse movement, or atypical navigation paths raise the fraud risk score and can trigger an automated block or challenge before any analyst reviews the case.
AI fraud detection in banking applies machine learning to transaction data, account behavior, and digital session signals to catch fraud before losses occur. Banks use it for card fraud detection, account takeover prevention, AML transaction monitoring, and synthetic identity fraud detection at onboarding. The approach reduces reliance on static rules and cuts the false positive rates that create unsustainable alert volumes for compliance and fraud operations teams.
AI fraud detection software combines machine learning models, behavioral analytics, device intelligence, and case management tools to detect and respond to financial fraud. Platforms like Sardine and Unit21 represent different priorities: Sardine emphasizes behavioral and device signals for session-level fraud, while Unit21 focuses on case management and rule customization for analyst-driven workflows. The right choice depends on whether your primary gap is signal quality or review workflow efficiency.
Machine learning fraud detection uses statistical models trained on historical fraud data to score new transactions and sessions in real time. The models improve continuously as they receive feedback on which flagged cases were real fraud versus false positives. This adaptive quality distinguishes machine learning from rule-based transaction monitoring systems, which require manual threshold updates each time fraud patterns shift.
Real-time fraud detection is the scoring and blocking of a fraudulent transaction within milliseconds of the event, before funds move. Banks implement it through low-latency scoring APIs that evaluate behavioral biometric signals, device fingerprints, and transaction details simultaneously during payment authorization. The allow, challenge, or block decision typically completes in 50-150 milliseconds on well-optimized stacks, fast enough to intervene before authorization is finalized.




Share this article