Listen To Our Podcast🎧

AML transaction monitoring rules tuning is where most financial institutions lose the compliance efficiency battle before it starts. If your alert queue has grown faster than your analyst headcount over the past two years, you are not alone. Industry estimates suggest that between 95% and 99% of transaction monitoring alerts are false positives, meaning your team investigates hundreds of transactions every week to catch a fraction of actual suspicious activity. The good news is that most of this waste is fixable through systematic tuning, better customer segmentation, and smarter use of aml compliance software that connects monitoring to customer risk profiles. This post walks through exactly how to tune your rules, reduce noise without raising regulatory risk, and build a program your team can realistically manage.
Why False Positives in AML Transaction Monitoring Are Getting Worse
The problem is not that your rules are wrong. It is that they were written for a different customer base, transaction volume, or risk environment than the one you are operating in today. Rules calibrated in 2020 or 2021 were not built for the behavioral patterns of customers using real-time payments, crypto on-ramps, or gig economy income structures. The rules kept running. The customers changed.
The Alert Volume Problem Nobody Talks About
Most compliance leaders track total alert volume, but fewer track the ratio of alerts to analysts or the time spent per investigation. When alert volume doubles and headcount stays flat, investigation quality drops. Analysts start pattern-matching shortcuts. Context gets skipped. That is where real risk lives: not in the alerts you miss, but in the alerts you close too quickly because there are simply too many of them.
As agentic AI fraud agents have demonstrated in practice, cutting false positives by 80% is achievable when you combine behavioral context with rule logic rather than relying on static thresholds alone.
What Drives Over-Alerting in Most Rule Sets
The most common culprits in over-alerting:
- Static thresholds that do not account for customer segment or historical behavior
- Single-factor rules that flag a transaction type without considering relationship context
- No suppression logic for known recurring patterns like payroll runs, rent payments, or authorized recurring transfers
- Missing peer group benchmarking, so a small business looks anomalous when compared against retail customers in the same data pool
Any one of these is manageable. All four together is what creates a 98% false positive rate.
How to Tune AML Transaction Monitoring Rules: A Step-by-Step Approach
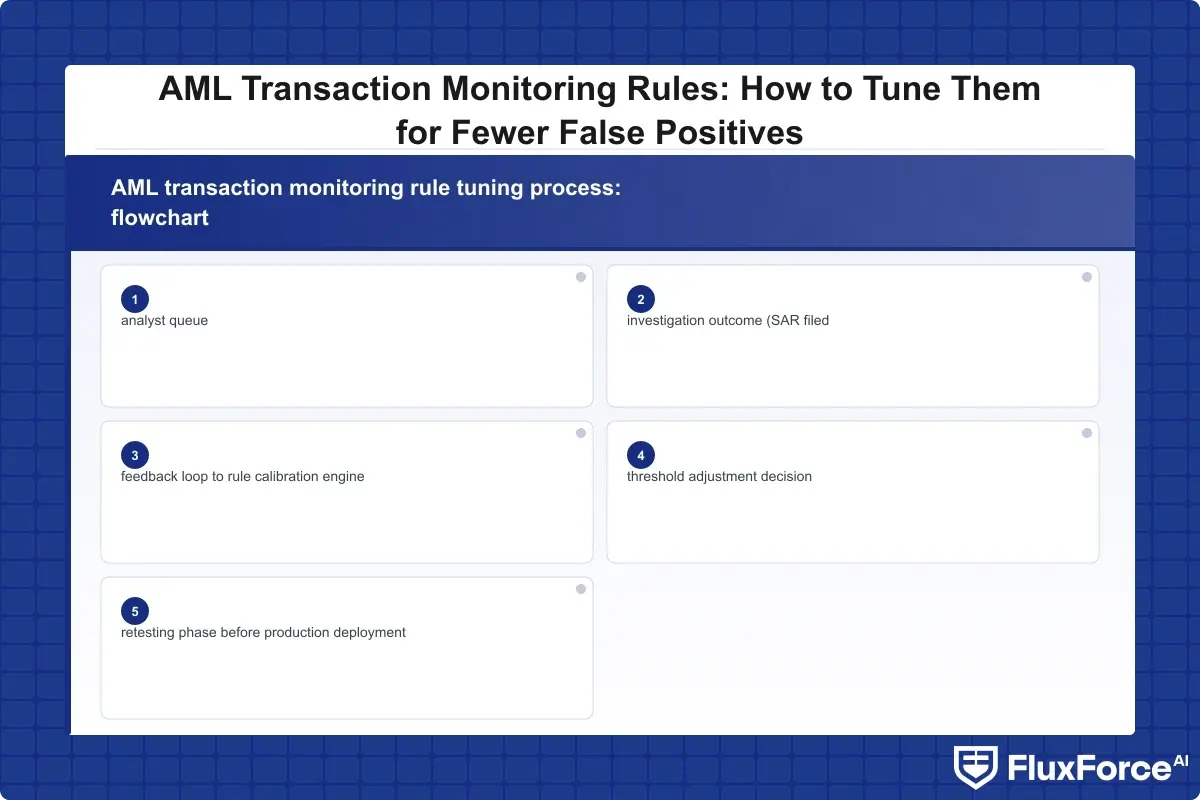
AML transaction monitoring rules tuning starts with data, not with rules. Before you adjust a single threshold, you need to understand why each rule is generating alerts and what percentage of each rule's alerts result in SARs versus closed investigations with no action taken.
Rule Types and Their False Positive Profiles
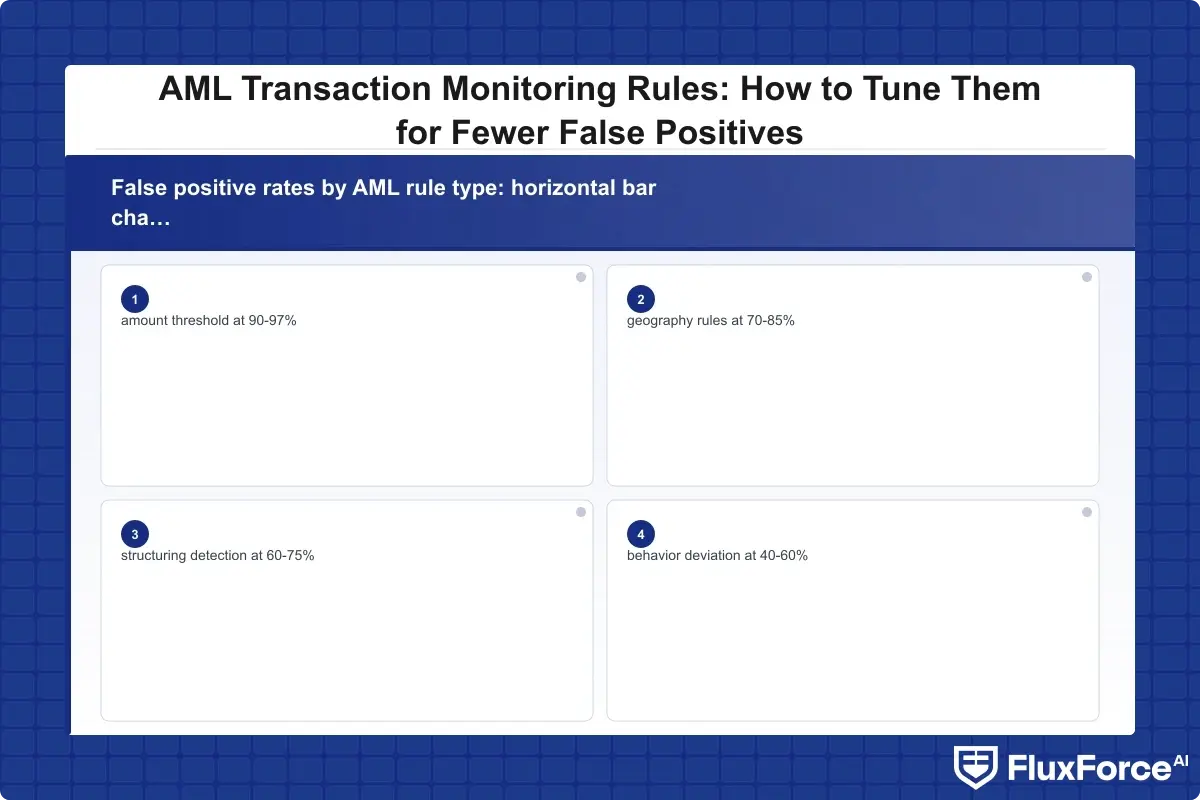
Most monitoring systems use a combination of these rule categories:
| Rule Type | Typical False Positive Rate | Primary Tuning Lever |
|---|---|---|
| Velocity rules (X transactions in Y days) | 85-95% | Shorten lookback window or add customer segment filter |
| Amount threshold rules | 90-97% | Adjust thresholds by customer risk tier |
| Geography/jurisdiction rules | 70-85% | Add whitelist for established counterparties |
| Structuring detection rules | 60-75% | Improve peer group context |
| Behavior deviation rules | 40-60% | Refine baseline calculation period |
Behavior deviation rules perform best because they are relative rather than absolute. A $50,000 wire from a corporate account that regularly processes $200,000 is a very different event from the same wire out of a retail savings account. That context is exactly what static threshold rules cannot capture.
Threshold Calibration: Where to Start
Start with your top five rules by alert volume. Pull 90 days of alert history for each and categorize outcomes: SAR filed, closed with no action, escalated, or pending. For any rule generating fewer than one SAR per 100 alerts, you have a calibration problem that deserves attention before anything else.
The fix is not always about raising thresholds. Sometimes the right answer is adding a suppression condition (exclude customers with a 24-month clean transaction history), changing segmentation (apply the rule only to accounts opened within 90 days), or requiring a second trigger before the alert fires.
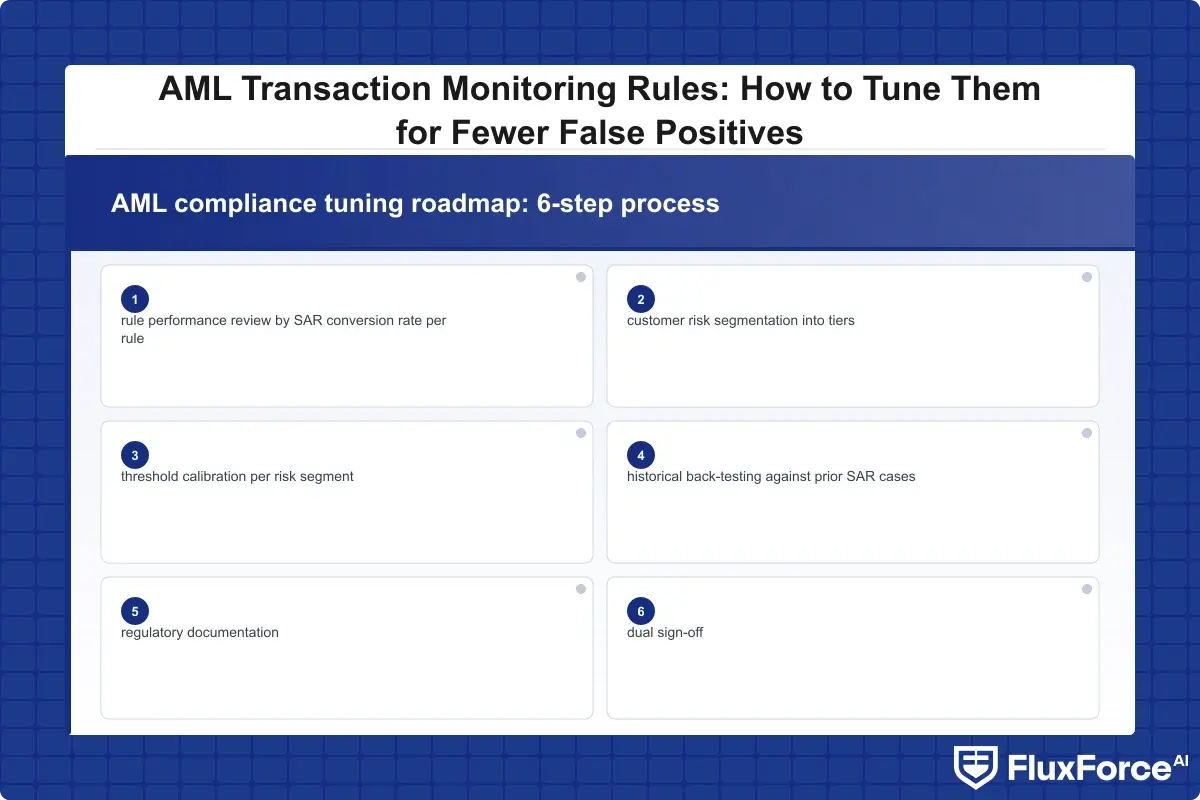
AML Risk Assessment Guide: Segmenting Your Customer Base First
Your monitoring rules should map to your risk tiers. Before touching any thresholds, segment your customers into at least three groups: low-risk, medium-risk, and high-risk. Each group should carry different alert sensitivity. A high-risk customer flagged by three different rules in the same week deserves immediate escalation. A low-risk customer flagged by the same combination probably needs a suppression review, not a full investigation.
This segmentation approach is also how you satisfy KYC and AML verification requirements in a way that is genuinely proportionate to actual risk rather than uniformly applied across your entire customer portfolio.
BSA AML Compliance Checklist for Rule Review
A functional bsa aml compliance checklist for rules tuning covers more than thresholds. It addresses the governance, documentation, and testing requirements that regulators expect to see when they examine your program.
An effective rule review checklist includes:
- Business justification documentation for each rule threshold, written in terms examiners can evaluate without your team present to explain it
- Statistical validation showing the rule detects a meaningful share of confirmed suspicious activity relative to total alerts generated
- Model risk management review if any rule uses statistical or machine learning components
- Change log with dual sign-off from compliance and a second reviewer outside the analyst team
- Back-testing evidence confirming the adjusted rule would not have suppressed alerts on historical SAR cases over the prior 12 months
- Escalation procedure for borderline cases that tuning creates ambiguity around
Tuning is a regulatory change, not just an operational one. If your documentation only says "we raised the threshold from $5,000 to $7,500," that is not enough to satisfy an examiner. You need the data that supported the decision.
BSA AML Compliance for Community Banks: Special Considerations
BSA AML compliance for community banks comes with specific pressure points that larger institutions do not face. Community banks typically operate with limited technology budgets, smaller compliance teams, and closer customer relationships, which creates both real challenges and genuine advantages.
The advantage: your analysts actually know your customers. A flagged transaction from a local business that your relationship manager knows runs a seasonal cash operation is much easier to contextualize. That relationship knowledge should be encoded into rule exceptions as formally documented suppression logic, not left as informal judgment calls that vary by analyst.
The challenge: many community banks run legacy core systems with limited API connectivity, making it harder to enrich alerts automatically with behavioral context. Manual enrichment steps can partially substitute, but they add meaningful time per case and create consistency risk.
Fintech BSA AML on a Small Team
Running a fintech BSA AML small team means you cannot absorb alert volume that a larger institution would distribute across a 20-person investigations unit. Your tuning needs to be especially precise because each investigation consumes a much larger share of total compliance capacity.
For aml compliance fintech organizations specifically, prioritize rules that are directly tied to SAR outcomes. Any rule that has not generated a SAR in 12 months should be reviewed for adjustment or retirement. That is not lowering compliance standards. It is recognizing that a rule producing zero SARs is either catching nothing actionable or generating alerts that do not meet the filing threshold, neither of which justifies analyst hours.
Anti Money Laundering Technology in 2026: What's Actually Useful
Anti money laundering technology has changed substantially over the past three years. The shift from static rule engines toward hybrid systems combining rules with machine learning has produced measurable results in institutions that have made the investment, though the implementation complexity is real and should not be underestimated.
Machine Learning vs. Rules: Finding the Right Balance
The honest answer on machine learning in AML is that it works better as a scoring layer than as a replacement for rules. Use ML to prioritize alerts, not to generate them unilaterally. A pure ML system without explainable rule logic will fail model risk management review at most regulated institutions, and for good reason: you need to explain your detection logic to examiners.
Anti money laundering technology 2026 is moving toward agentic workflows: systems that not only score alerts but also gather supporting context, including prior transaction history, open-source news, and sanctions list status, before the alert reaches an analyst. This is where regulatory compliance automation is creating the biggest efficiency gains, by eliminating the manual context-gathering that currently consumes 40-60% of analyst time per investigation.
The architecture that works: rules generate alerts, ML scores and ranks them, automation gathers supporting context. Analysts spend their time on judgment calls, not on pulling data from three separate systems before they can begin the actual investigation.
EU AI Act Financial Services Impact
The EU AI Act financial services obligations matter for any institution operating in European markets. AML transaction monitoring systems using AI components may fall under the high-risk AI system classification, which triggers additional requirements around model documentation, human oversight, and output explainability.
If you are using ML-based scoring in your monitoring, you need an explainability layer that can demonstrate how a specific score was calculated. Systems that cannot produce that explanation carry regulatory liability under implementation timelines running through 2025-2026. The official EU AI Act framework covers full requirements and applicable timelines.
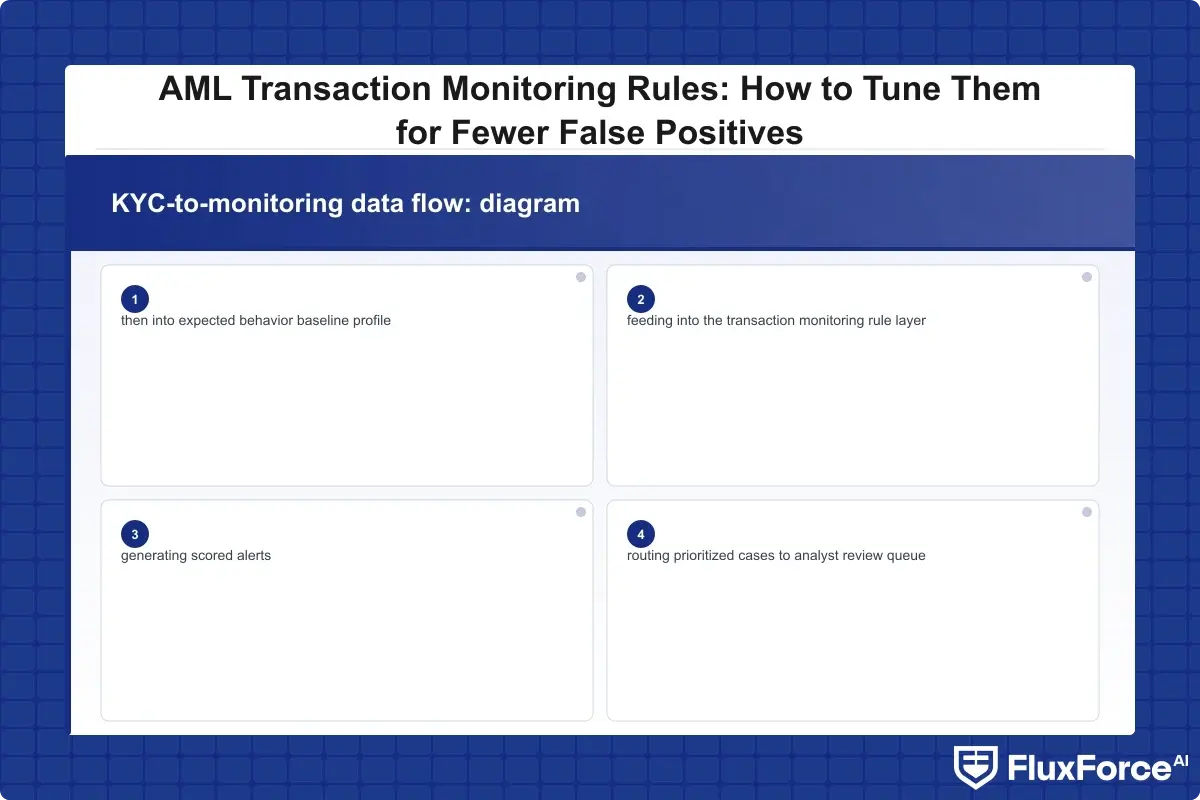
KYC Automation and CDD: The Missing Link in Alert Tuning
Your transaction monitoring rules can only be as good as the customer data feeding them. Weak KYC means inaccurate baseline behavior models, which means worse alert quality regardless of how carefully your thresholds are set. This is why kyc automation initiatives and monitoring tuning need to be coordinated programs, not separate workstreams.
KYC CDD Requirements for Banks in Practice
KYC CDD requirements for banks cover four core elements under FinCEN's Customer Due Diligence Rule: customer identification, beneficial ownership identification, understanding the nature of the customer relationship, and ongoing monitoring. The last element connects directly to transaction monitoring rule quality in ways that most institutions have not fully operationalized.
If your CDD process captures expected transaction volume and types at onboarding, that data should feed directly into your monitoring baseline. A business customer onboarded with an expected monthly transaction volume of $50,000 should not be triggering alerts at $45,000 unless other risk factors are simultaneously present.
Enhanced Due Diligence Guide for High-Risk Customers
An enhanced due diligence guide for high-risk customers should include more frequent review cycles, source-of-funds documentation, and in some cases a separate monitoring rule layer with lower thresholds. If your EDD customers are monitored under the same rules as standard customers, you have a structural gap: the same alert that appropriately gets closed on a low-risk customer may require mandatory escalation on an EDD customer.
A practical fix: create a separate rule set for EDD customers with lower alert thresholds and a mandatory escalation step for any pattern that would normally be suppressed under standard customer monitoring rules.
KYC Automation 2026: What Changes This Year
KYC automation 2026 is seeing faster adoption of identity verification at onboarding feeding directly into live monitoring profiles. Institutions that have connected their KYC platform to their monitoring system report measurable alert quality improvements because behavioral baselines are captured accurately from day one. The integrated AML screening approach in digital lending shows how connected KYC-monitoring workflows reduce both false positives and onboarding friction at the same time.
SAR Filing Efficiency: Tuning Rules to Reduce Your Filing Burden
Better-tuned rules do not just reduce analyst workload. They improve SAR filing efficiency by ensuring the alerts that reach analysts are genuinely worth investigating. SAR quality, not just SAR count, is what regulators assess during examinations. A program filing 50 well-documented SARs looks very different from one filing 200 marginal ones.
Suspicious Activity Report Guide: When to File vs. When to Close
The decision framework in any practical suspicious activity report guide is more straightforward than most teams make it:
- Does the activity meet the dollar threshold ($5,000 for banks, $2,000 for money services businesses, per FinCEN guidance)?
- Is there a reasonable basis to believe the transaction involves proceeds from illegal activity, is structured to evade reporting, or lacks a lawful explanation?
- Have you documented the investigation clearly enough that a regulator could reconstruct the decision trail independently?
If the answer to any of these is unclear, file. SAR filing best practices consistently favor filing with incomplete information over not filing and missing a pattern. You can amend a SAR; you cannot retroactively file one after the window closes.
SAR Filing Requirements 2026
SAR filing requirements 2026 include a 30-day deadline from the date of initial detection (90 days when no suspect is identified at time of detection), with mandatory fields covering the type of suspicious activity, subject information, and transaction details. FinCEN currently recommends joint filings for connected financial institutions where suspicious activity crosses multiple entities, which is particularly relevant for bank-fintech partnerships where monitoring responsibilities are split across two compliance programs. Reference the FinCEN SAR filing guidance for current thresholds and required field specifications.
What AML Compliance Software Should Actually Do
AML compliance software is not a substitute for well-calibrated rules, but the right platform makes tuning faster, more auditable, and easier to defend during examinations. The functional requirements that matter most:
- Alert disposition tracking with full investigator notes and documented decision rationale per case
- Rule performance dashboards showing SAR conversion rates per rule over configurable time windows
- Threshold testing against historical alert data before changes go live in production
- Audit trails showing when rules changed, who approved changes, and the supporting data rationale
- Integration with KYC data to enrich alerts automatically before they reach an analyst
AML Compliance Fintech: Platforms Built for Scale
AML compliance fintech platforms designed for scaling organizations handle the specific challenge of rapid customer onboarding alongside transaction monitoring at high volume. The critical difference from traditional bank-facing tools is real-time processing capacity: fintech transaction volumes can spike significantly within hours, and monitoring systems need to scale without generating proportional alert volume increases alongside that spike.
Test any platform against your peak volume scenario, not your average daily volume. A system performing well at 1,000 transactions per day may degrade badly at 10,000, and that is exactly when reliable performance matters most. For compliance teams deciding whether to invest in additional rule sophistication or AI scoring, the comparison of rule-based systems vs. AI-driven approaches is a useful framework for structuring that decision.
CTR Filing Rules and How They Interact with Monitoring
CTR filing rules require currency transaction reports for cash transactions exceeding $10,000 in a single business day. The overlap with transaction monitoring is that CTR-generating transactions frequently also trigger monitoring rules, creating duplicate analyst touches on the same event with no additional compliance value.
A clean AML program suppresses the monitoring alert when a CTR is automatically generated, avoiding unnecessary investigation time on a transaction already being reported through the required regulatory channel. This suppression logic should be explicitly documented and tested regularly. When tuning monitoring rules, always verify that CTR suppression is functioning correctly, particularly if you are making threshold changes near the $10,000 boundary.
Onboard Customers in Seconds

Conclusion
AML transaction monitoring rules tuning is not a one-time project. It should run on a 90-day review cycle at minimum, with major rule changes going through formal validation, back-testing, and dual sign-off documentation. The compliance programs that manage false positives well are not necessarily running more sophisticated rules than yours. They are reviewing and adjusting their rules more systematically, with better data behind each decision.
Start with your highest-volume rules and measure SAR conversion rates per rule. Segment your customers before touching any thresholds. Connect your kyc automation data to your monitoring baselines so that expected behavior is encoded at onboarding, not inferred retroactively from early transaction history. Document every threshold change with the supporting analysis.
AML compliance is ultimately about finding actual bad actors in your customer portfolio. Every hour an analyst spends closing a false positive is an hour not spent on a genuine suspicious case. Better-tuned rules and well-integrated anti money laundering technology are how you recover that capacity and make your program more effective at the same time.
Frequently Asked Questions
AML compliance (Anti-Money Laundering compliance) is the set of policies, procedures, and controls that financial institutions use to detect, prevent, and report money laundering activity. It includes customer due diligence, transaction monitoring, suspicious activity reporting, and employee training, all governed primarily by the Bank Secrecy Act in the US and equivalent regulations internationally. Effective AML compliance connects risk-based customer segmentation to monitoring rule sensitivity so that analyst effort is directed toward genuinely suspicious activity rather than false positives.
AML compliance in fintech covers the same core requirements as traditional banking (KYC, transaction monitoring, SAR filing) but applied to digital-first business models that onboard customers at higher velocity without in-person verification. AML compliance fintech programs rely more heavily on automated monitoring tools and aml compliance software to compensate for smaller compliance teams relative to customer volume. BSA obligations apply equally to fintech companies with money transmitter licenses, banking-as-a-service integrations, or chartered bank partnerships.
A BSA AML compliance checklist is a structured review framework covering the five pillars of an effective BSA/AML program: internal controls, a designated compliance officer, ongoing employee training, independent testing, and customer due diligence procedures. For transaction monitoring specifically, the checklist should also include rule performance metrics showing SAR conversion rates per rule, change documentation with dual sign-off, and back-testing evidence for any threshold adjustments made during the tuning process.
BSA AML compliance for community banks refers to the Bank Secrecy Act obligations applied to smaller, locally-focused financial institutions operating under the same regulatory framework as larger banks. Community banks face identical core requirements but typically with fewer technology resources and smaller compliance teams. This makes systematic rules tuning especially important: each analyst hour is more constrained, and the advantage of direct customer relationship knowledge should be encoded into monitoring rule exceptions to reduce unnecessary alert volume.
AML compliance software is a technology platform that automates transaction monitoring, alert management, SAR and CTR filing workflows, and customer risk scoring. Effective aml compliance software includes configurable rule engines with performance dashboards showing SAR conversion rates per rule, audit trails for regulatory examination, threshold testing against historical data before production changes, and integration with KYC systems to enrich alerts automatically with customer context before they reach an analyst for investigation.
Anti money laundering technology covers the tools and systems used to detect and prevent financial crime, including transaction monitoring platforms, behavioral analytics engines, sanctions screening tools, and KYC automation solutions. Anti money laundering technology 2026 increasingly includes AI-based alert scoring layers and agentic workflow automation that gather investigation context automatically before alerts reach human analysts, reducing the manual data-gathering that currently consumes 40-60% of investigation time at most institutions.
SAR filing requirements in 2026 include a 30-day deadline from the date of initial detection (90 days when no suspect is identified at time of detection), mandatory fields covering transaction details, subject information, and activity type, and a $5,000 threshold for bank filings ($2,000 for money services businesses). FinCEN currently recommends joint filings where suspicious activity spans multiple financial institutions, which is particularly relevant for bank-fintech partnerships where transaction monitoring may be split across two separate compliance programs with different rule sets.






Share this article