Listen to our podcast 🎧
.png)
Introduction
Mobile banking has changed the way people handle their money. Today, people prefer using banking apps instead of visiting a branch. Mobile-first banks focus on apps and digital tools as the main way customers access their accounts. This brings convenience, but it also introduces new mobile banking security risks. Unlike traditional banks, mobile-first banks work across many devices and networks, which can make them easier targets for hackers and fraud.
According to a survey, over 70% of financial services firms face insider threats, making strong security a must for banks.
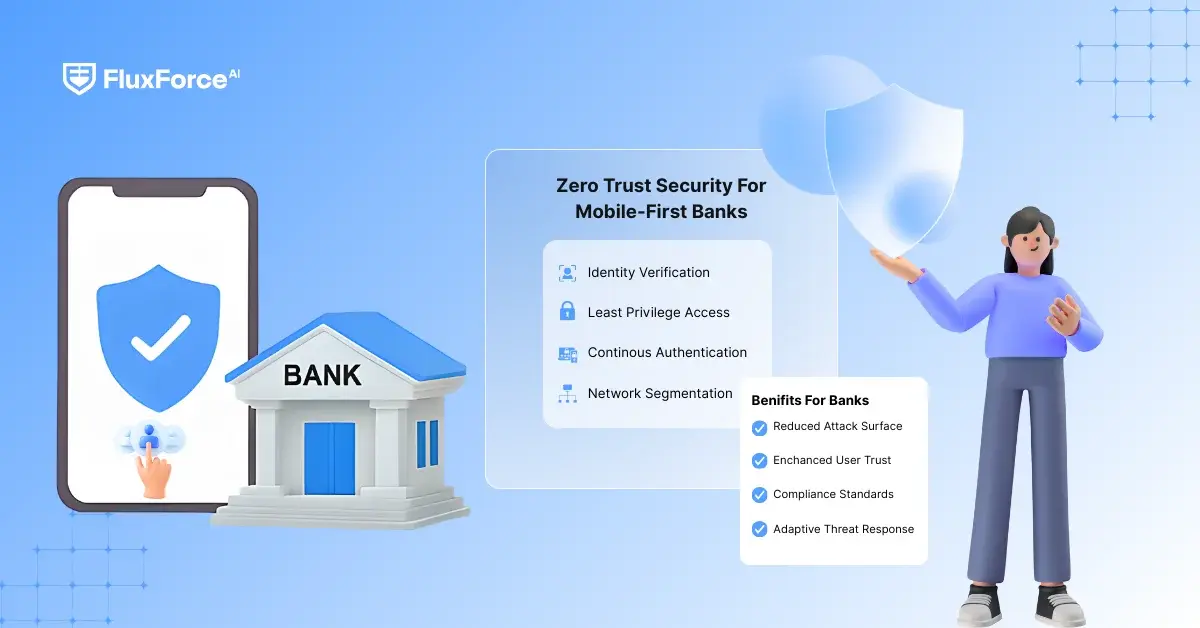
What is Zero Trust Security?
Zero Trust Security is a modern way to protect systems that assumes no user, device, or network can be trusted by default. Every access request must be verified before allowing entry. Old security systems usually trust people once they are inside the network, but Zero Trust security works the other way: never trust, always check.

For mobile-first banks, Zero Trust is important because:
- Mobile banking apps are used on public Wi-Fi and other networks, which increases risk.
- Customers expect fast, easy access, so security must remain seamless.
- Employees and attackers can steal credentials, making continuous verification essential.
John Kindervag, who created the Zero Trust model, says:
"Security cannot depend on where a user is. Zero Trust assumes there might already be a breach and protects everything."
Why Mobile-First Banks Are at Risk?
- Mobile Fraud: Banking apps are targeted by malware, phishing, and account takeover attacks. The FBI reported that mobile banking fraud went up by more than 50% in 2024.
- Many Devices and Networks: Many devices and networks: Mobile banking apps are used on smartphones, tablets, and smartwatches, often on public networks. Each device can be a way for hackers to get in.
- Customer Trust: One security data breach can hurt the bank’s reputation and make customers lose trust. Maintaining strong mobile banking security is now essential for business continuity.
How Zero Trust Helps
Zero trust security in mobile banking means: :
- Continuous Verification Banking: Every user and device is continuously verified, not just at login.
- Micro-Segmentation of Networks: Banking network micro-segmentation splits systems into small secure sections, so even if one part is attacked, the damage is limited.
- Identity-Centered Security: Only verified users can access sensitive data, supporting identity-centric security for banks across devices and locations.
A study by Gartner found that banks using zero trust security saw a 50% drop in security incidents.
Banking Systems and Infrastructure
Mobile-first banks need to update their retail banking architecture to implement zero trust security effectively. Traditional systems built for branch banking cannot handle real-time mobile banking access securely. Banks need modern systems, cloud services, and secure APIs to support continuous verification and banking network micro-segmentation.
Next, we will look at remote identity verification and continuous security in mobile banking, showing how banks can prevent unauthorized access and fraud.
Identity Verification and Continuous Security in Mobile Banking
In mobile banking, proving who the customer really is the most important step in ensuring secure access. That’s why banks are moving beyond just usernames and passwords. They now use remote identity verification and continuous checks to keep accounts safe.

Remote Identity Verification: The First Step
Remote ID verification allows people to prove their identity without visiting a branch. For example, a customer can scan their driver’s license or passport using their mobile device. With tools like trust ID mobile, banks can verify if the ID is real and match it with a live selfie of the customer.
This form of remote identity verification is becoming very common in banking. A report by Jumio found that 1 in 3 banking customers want a fully digital way to prove their identity.
Adding Device Reputation Checks
Fraud doesn’t always come from fake IDs. Sometimes, it comes from stolen or risky devices. This is where device reputation verification comes in. The system checks if the device has a history of fraud or suspicious activity . If yes, the bank can block access or ask for extra checks.
Identity Verification on Mobile: Different Methods
Banks use multiple mobile identity verification methods to ensure the person logging in is the real account holder:
- Biometrics: Face or fingerprint scan (easy and safe).
- App Push Notifications: Safer than SMS, since the check happens inside the banking app.
- Behavioral Biometrics: Looks at typing speed, touch patterns, or how someone holds their phone.
Old systems only checked users when they logged in. But with continuous verification, banks now keep checking during the session. For example, if a customer logs in from one country but suddenly switches to another, the system may ask for extra proof.
This approach is part of identity-centric security for banks, which means focusing on the person and their device, not just the network they’re on.
Gartner says: “By 2026, 80% of digital businesses will require continuous checks for both customers and employees to cut down fraud and insider risks.”
Banks are also using remote identity verification to make account recovery easier . If someone forgets their password, they don’t have to visit a branch. Instead, they can prove their identity again using their phone.
This makes life easier for customers and also reduces work for banks.
Zero Trust Security for Banking Networks and Mobile Systems
Why Traditional Banking Security Fails in Mobile-First Banking ?
Old “castle-and-moat” models trusted anyone inside the network. But in today’s mobile-first banking environment, customers connect through mobile banking apps, home Wi-Fi, and even public hotspots. This exposes weak spots in banking network infrastructure, giving hackers easy ways to slip in and cause damage.
With mobile fraud rising, relying on outdated defenses is too risky for banks.
How Zero Trust Strengthens Banking Network Security ?
Zero trust security flips the script: no one is trusted until they are verified. For mobile-first banking security, this approach ensures every customer, employee, and device must prove their identity before accessing sensitive data.
Banks apply zero trust security across three major areas:
Banking Network Micro-Segmentation
Splitting the network into smaller parts stops hackers from moving freely once inside.
Privileged Access Management in Banking
Privileged access management in banking ensures employees only access the systems they truly need, reducing insider risks.
Endpoint Security Strategies for Mobile-First Banks
Every phone, tablet, or laptop is scanned for security issues before being allowed to connect.
Proof That Zero Trust Works in Financial Services
- As per IBM’s 2023 Cost of a Data Breach Report, banks with Zero Trust saved almost $1M per breach compared to banks without it.
- Microsoft Security Blog highlights: “Zero Trust is now the top security priority for financial services organizations, especially as mobile banking adoption grows.”
Clearly, Zero Trust for banking is delivering both cost savings and stronger protection.
Future of Secure Mobile Banking Access with Zero Trust
In the coming years, zero trust security will work hand-in-hand with AI and automation to make mobile banking safer and more seamless. Banks will likely expand:
- Risk-based authentication for mobile banking users that adjusts checks based on unusual behavior.
- Continuous verification in banking sessions to spot and stop fraud in real time.
- Password-less and secure mobile banking access for better customer experience.
With banking network micro-segmentation, privileged access management, and strong endpoint security strategies, banks can build a secure mobile banking security framework for the future.
Real-World Case Studies of Zero Trust in Mobile-First Banks
Banco Inter (Brazil): Securing a Digital-Only Bank with Zero Trust
Banco Inter, Brazil’s first fully digital bank, serves over 40 million customers mainly through its mobile platform. To keep operations safe, the bank turned to Zero Trust using Zscaler’s Zero Trust Exchange.
The bank secured internet use, private app access, and encrypted all customer traffic. It also extended protection to cloud services and AI tools like InterGPT. This gave Banco Inter a strong and flexible base to grow its mobile-first services while keeping customer data secure.
Source: SiliconANGLE
FirstBank (Romania): Faster Mobile Onboarding with Remote Identity Checks
FirstBank wanted to make account opening easier for mobile users. The bank moved away from slow, manual checks and adopted Entrust’s document and video-based identity verification.
This change cut onboarding time from two days to just eight minutes. Now, customers can safely open accounts and access banking services on their phones without visiting a branch. The process follows Zero Trust by confirming each user’s identity before granting access.
Source: Entrust
Shinhan Bank (South Korea): Mobile Banking Made Safer with Biometrics
Shinhan Bank, one of South Korea’s largest banks, upgraded its mobile app with FIDO-based authentication. Through the Sunny Bank app, customers can log in and manage services like account opening and loans using fingerprint or facial recognition.
This approach removed the need for passwords, lowered fraud risks, and made banking simpler for customers. By using mobile identity verification methods, Shinhan Bank improved both security and trust.
Source: FIDO Alliance
Key Takeaways from Mobile-First Banks
These case studies show how mobile-first banks are applying Zero Trust in practice:
- Banco Inter strengthened its digital services and AI with Zero Trust.
- FirstBank used remote identity verification to make onboarding faster.
- Shinhan Bank adopted biometrics to make mobile access safer.
Together, they prove that Zero Trust security solutions for mobile-first banks can protect customer data, reduce fraud, and support safe digital growth.

Shaping the Future of AI in Finance
Fluxforce research uncovers how banks and enterprises are adapting to fraud, compliance, and data challenges in 2025.
The Future of Zero Trust Security in Mobile-First Banking
Mobile-first banking is now the main way many people use financial services. But with more mobile use comes bigger risks like identity theft, account takeovers, and mobile fraud. This is why Zero Trust security is becoming the key part of mobile banking security strategies.
IBM’s Cost of a Data Breach Report 2023 shows that the average data breach in finance costs about $5.9 million. Juniper Research says global payment fraud losses may cross $343 billion from 2023 to 2027. These numbers show why mobile-first banks must act fast.
How Zero Trust Will Shape Mobile Banking Security
- Continuous Verification: Instead of checking only at login, banks will confirm identity at every step.
- Risk-Based Authentication: Users face extra checks only if their activity looks unusual.
- Device Reputation: Banks will block unsafe devices like rooted or infected phones.
- Stronger Mobile Identity Verification Methods: Biometrics, video checks, and document scans will become common.
- Micro-Segmentation in Banking Networks: Dividing systems into smaller parts will limit damage if a breach happens.
Moving Toward Identity-Centric Security
For mobile-first banks, security will focus on identity—checking the person, the device, and the situation before giving access. Managing employee access and keeping mobile banking safe for customers will be core steps.
As John Kindervag, creator of Zero Trust, said: “Never trust, always verify. Security must become the default position.”
Strengthen Trust in Global Trade

Conclusion
Zero Trust in banking is not a one-time setup. It requires ongoing updates, testing, and monitoring because new risks appear every day. For mobile-first banks, this approach is not just about protecting data. It also helps create smoother mobile services, faster onboarding, and stronger customer confidence.
Banks that adopt Zero Trust can move forward with more freedom to innovate because security is built into every step. By combining strong identity checks, safer devices, and smarter mobile fraud prevention, they can grow in the digital world while keeping customer trust at the center.






Share this article